Trezor.io/Start: Secure Your Crypto Step by Step
Beginner to intermediate guide for Trezor hardware wallets and best security practices.
Why Hardware Wallets Are Essential
Hardware wallets like Trezor act as a secure vault for your crypto keys. Unlike software wallets or exchanges, private keys never touch the internet, protecting your funds from hacks, malware, and phishing attacks. Starting at trezor.io/start ensures you follow official, safe instructions.
Step 1: Unbox & Inspect
- Check for tamper-evident seals.
- Verify serial numbers on the device and packaging.
- Use only the official USB cable.
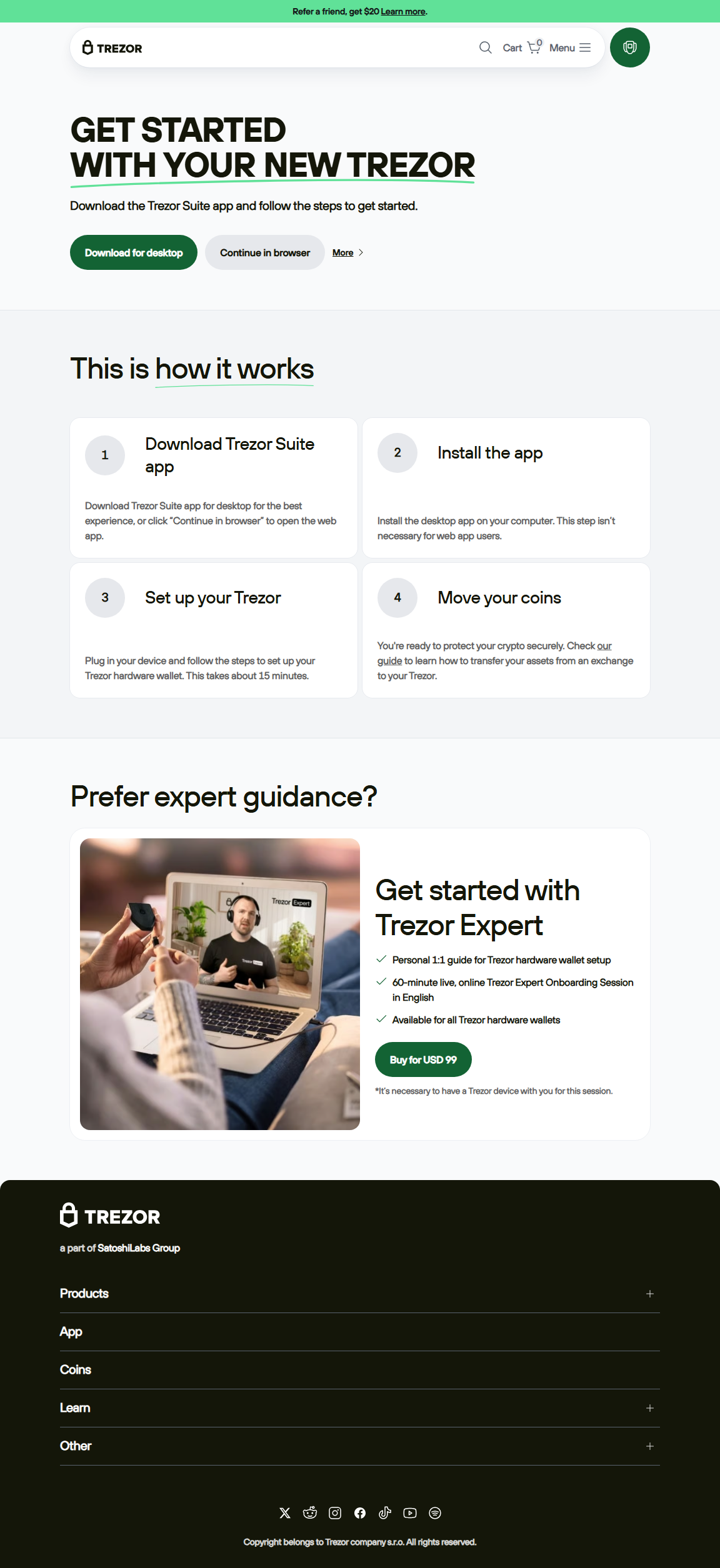
Step 2: Visit trezor.io/start
Enter the URL directly in your browser. Download the Trezor Suite for your operating system. Avoid search engines or ads to prevent phishing attacks.
Step 3: Install Firmware
Follow prompts in Trezor Suite to install the official firmware. The device verifies the signature on-device to ensure it’s authentic.
Step 4: Wallet Creation & Backup
Generate a 12, 18, or 24-word recovery seed on your Trezor. Write it down physically—never take photos or store it digitally. For Trezor Model T, Shamir Backup allows splitting the seed into multiple parts for extra redundancy. Always test your backup on a secondary device if possible.
Step 5: Send & Receive Crypto
- Receive funds by copying the address from Suite and verifying it on the device.
- Send crypto by confirming recipient, amount, and fees on-device.
- Advanced: use coin control, passphrase wallets, or multisig setups for large amounts.
Pro Tips
- Always verify addresses on-device.
- Keep firmware up to date.
- Backup your seed offline.
- Consider multisig or passphrase wallets for large holdings.
Security Comparison
| Feature | Trezor (Hardware) | Software Wallet |
|---|---|---|
| Private Key Exposure | Never leaves device | Stored online or in OS |
| Phishing Risk | Low, verified on-device | High, URL spoofing possible |
| Backup & Recovery | Seed phrase / Shamir optional | Depends on software |
FAQs
Q: Can I recover my wallet if the Trezor is lost?
A: Yes, using the recovery seed you created. Restore it on a new device.
Q: Can Trezor be hacked remotely?
A: No. Keys never leave the device; hacks usually involve social engineering or seed exposure.
Q: Difference between Model One & Model T?
A: Model T has a touchscreen, Shamir backup, and more coin support; Model One is simpler and cheaper.
Final Thoughts
Starting at trezor.io/start gives you full control of your crypto. Follow these steps carefully, back up your seed offline, and explore passphrase or multisig options for added security.
Your Trezor becomes a digital vault — secure your crypto confidently today.